Introduction
Today, mobile devices are ubiquitous within enterprise environments. But with their proliferation, it provides adversaries with yet another attack surface with which they can target users and cause a breach.
From phishing attacks to malicious apps, mobile users tend to let their guard down and potentially click on obfuscated links to malicious sites. Falcon for Mobile protects users by preventing connections to malicious sites on both iOS and Android devices. Some examples of sources for these malicious connections are texts, emails, apps, or even QR codes.
Falcon for mobile can block navigating to malicious sites and notifying the user why it was blocked, educating the user and reducing the risk in the future.
Security administrators can also view reports within the Falcon Console to identify individuals within the organization that may require additional phishing training.
Video
Protecting Mobile Users
When the device attempts to connect to the site, we see that it cannot be reached. The user is protected from the site if it was an attempt to harvest their credentials or collect their data.
Falcon for Mobile also provides a notification as to why the site was blocked. The user can expand the notification to see additional details.
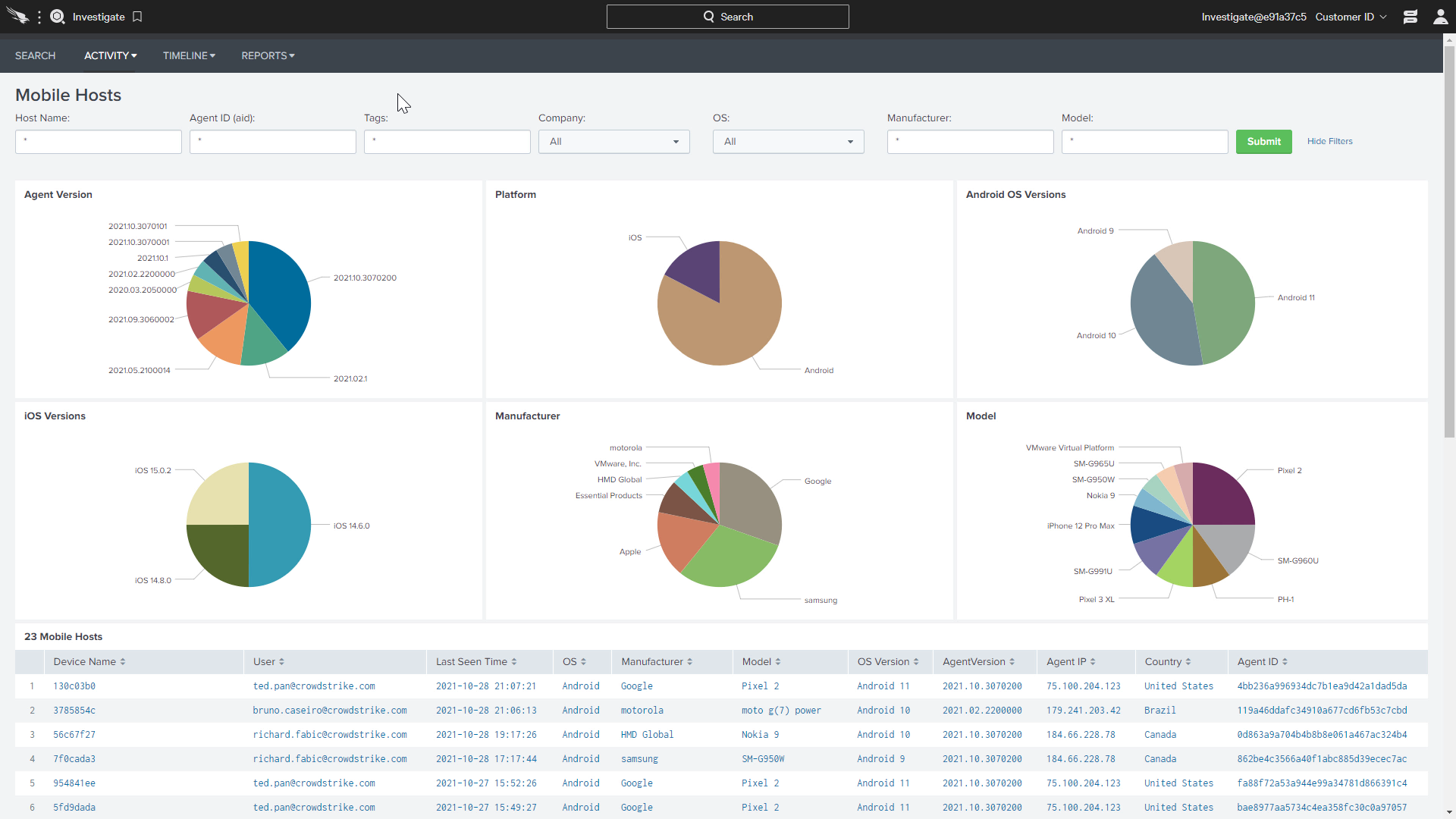
The Falcon Console can show details on the various models and software versions on the mobile devices leveraged by the organization. This would be a good place to see if any devices may need to be updated.
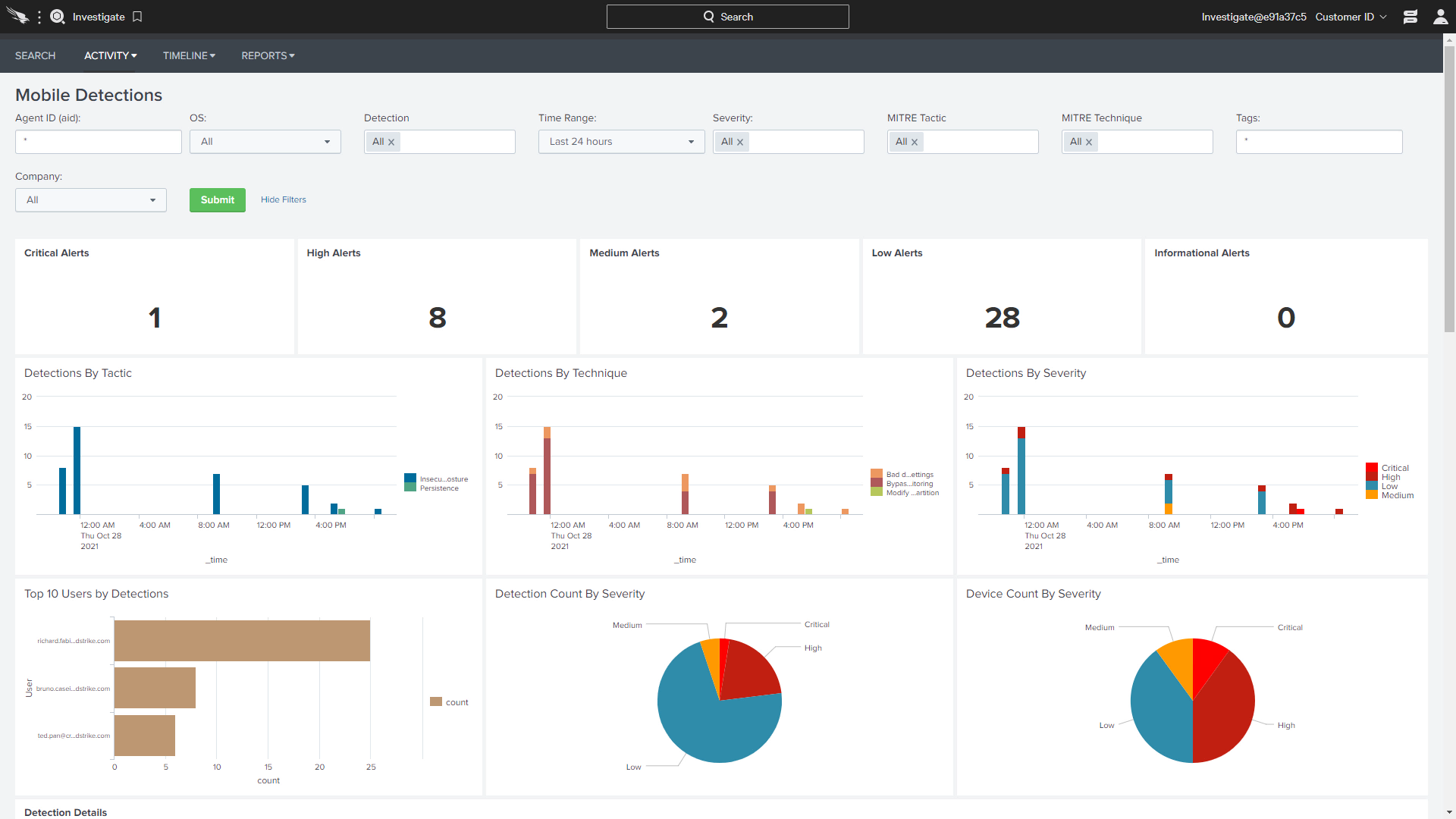
The Mobile Detections show a dashboard with an overview of detections including alert severity, tactics and technique, and the device user.
Conclusion
So as we can see, Falcon for Mobile provides powerful protection that prevents users from unknowingly navigating to malicious sites and accidentally sharing data or credentials .
With phishing attacks being such a common vector for mobile attacks, blocking malicious network connections with Falcon for Mobile helps protect organizations from a breach.
More resources
Go to Source
Author: Ted Pan

